PS1 Cannot Be Loaded Because Running Scripts Is Disabled | Reasons and Solutions
When attempting to execute PowerShell scripts, users may encounter the error message “PS1 Cannot Be Loaded Because Running Scripts Is Disabled.” This error arises due to a security measure implemented by PowerShell to prevent unauthorized script execution.
Here goes the ‘why’s and ‘how’s on it.
Root Cause Analysis: Why Scripts Are Disabled by Default
PowerShell enforces script execution restrictions to safeguard against malicious scripts that could harm the system or compromise sensitive data. By default, PowerShell execution policies prevent the execution of unsigned scripts, those without a digital signature from a trusted publisher.
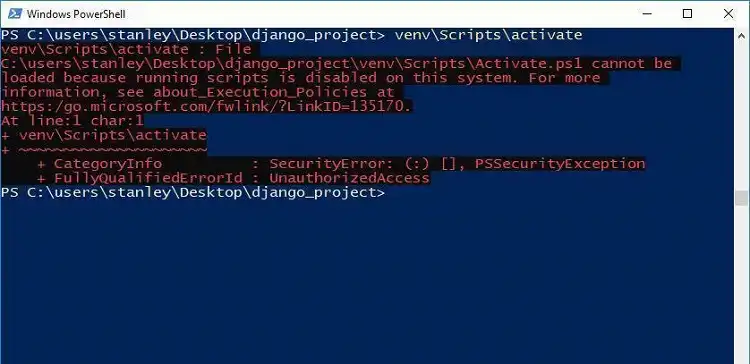
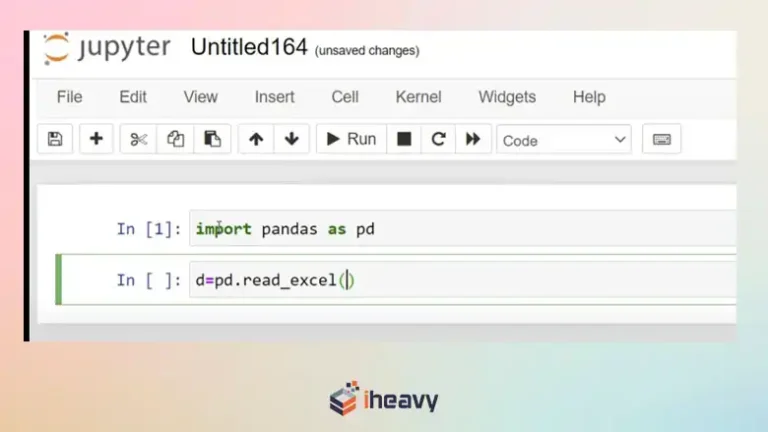
Figure 1: PowerShell error message PS1 Cannot Be Loaded Because Running Scripts Is Disabled Opens in a new window
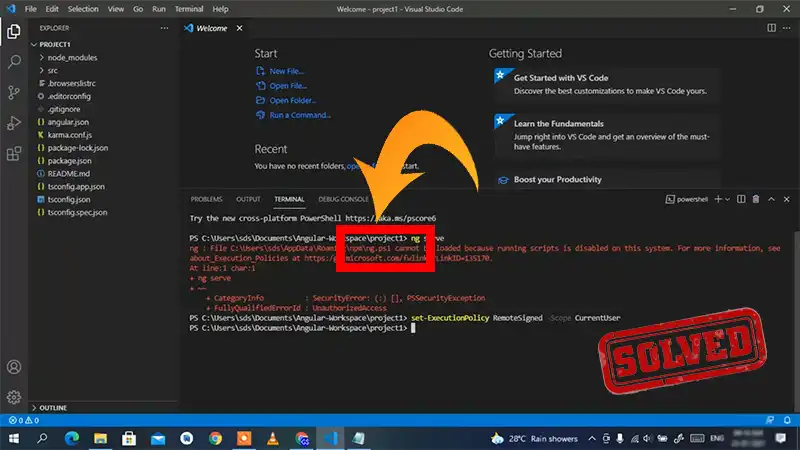
Resolving the Error: Enabling Script Execution for Specific Purposes
To execute the desired script, users need to adjust the PowerShell execution policy. This can be done by opening PowerShell with administrative privileges and running the command “Set-ExecutionPolicy RemoteSigned.” This allows execution of scripts digitally signed by remote publishers.
Execution Policy Options
PowerShell offers several execution policy options:
- RemoteSigned: Allows execution of scripts digitally signed by remote publishers.
- AllSigned: Allows execution of scripts digitally signed by any publisher, including the local machine.
- Bypass: Allows execution of all scripts, regardless of their digital signature status.
- Unrestricted: Allows execution of all scripts, including unsigned scripts, and disables script execution logging.
Selecting the Appropriate Execution Policy: Balancing Security and Functionality
The choice of execution policy depends on the specific requirements and security posture of the organization. While a more restrictive policy enhances security, it may limit legitimate script execution. A less restrictive policy may increase functionality but also introduce security risks.
Setting Execution Policy for Current User or All Users
While enabling script execution allows for the desired functionality, it introduces potential security risks. Malicious scripts could still be executed if they are digitally signed by a trusted publisher. Users should exercise caution and only execute scripts from trusted sources.
The execution policy can also be set for the current user or all users. For the current user, use the command “Set-ExecutionPolicy RemoteSigned -Scope CurrentUser.” For all users, use “Set-ExecutionPolicy RemoteSigned -Scope MachinePolicy.”
Utilizing Group Policy Objects for Enterprise-Wide Script Execution Management
In enterprise environments, Group Policy Objects (GPOs) can be employed to manage script execution policies across multiple computers. This centralized approach simplifies policy administration and ensures consistency across the organization.
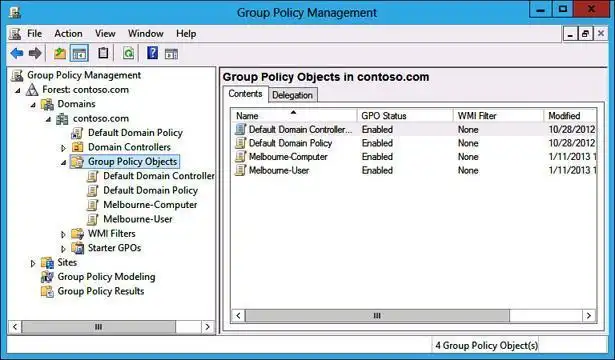
Figure 2: Group Policy Object (GPO) in Windows Server Opens in a new window
Enhancing Security Measures: Implementing Additional Safeguards
Alongside execution policy management, organizations should implement additional security measures, such as user access controls, script logging, and regular security audits, to minimize the risk of unauthorized script execution.
Striking a Balance: Achieving a Secure Script Execution Environment
By carefully evaluating execution policy options, implementing additional security measures, and educating users about script execution risks, organizations can strike a balance between script execution functionality and system security.
Frequently Asked Questions
Why is running scripts disabled in PowerShell by default?
PowerShell has a default security policy that restricts script execution to prevent the accidental or malicious running of scripts. This is a security measure to protect the system.
Are there different execution policies in PowerShell?
Yes, PowerShell provides various execution policies, such as Restricted, AllSigned, RemoteSigned, Unrestricted, etc. Each policy has different levels of restrictions on script execution.
Can I enable script execution for a specific script only?
Yes, you can bypass the execution policy for a specific script by using the -ExecutionPolicy parameter when running the script. For example, you can run powershell -ExecutionPolicy Bypass -File script.ps1.
Is it recommended to change the default execution policy?
Changing the execution policy should be done cautiously, considering security implications. It’s generally recommended to only modify the policy after understanding the potential risks and ensuring scripts are from trusted sources.
What should I do if I encounter this issue in a restricted environment where I can’t change the execution policy?
In some cases, you might need to work with system administrators to modify the execution policy or find alternative ways to run scripts, such as using signed scripts.
Can Group Policy settings affect script execution in PowerShell?
Yes, Group Policy settings can override local PowerShell execution policies. If your system is part of a domain, group policies might be enforcing script execution restrictions.
How can I check the current execution policy in PowerShell?
You can use the Get-ExecutionPolicy cmdlet to check the current execution policy. Running this command will display the current policy level set on the system.
Conclusion
PowerShell’s script execution restrictions protect against malicious scripts. By enabling script execution selectively and implementing additional security measures, organizations can achieve a balance between functionality and security.



![Comparing Cloudflare and AWS WAF | [Answered]](https://www.iheavy.com/wp-content/uploads/2024/05/Comparing-Cloudflare-and-AWS-WAF-768x432.webp)